One of the lingering impressions I have of the NHS is of an organization that’s cornered the market in laser-printer labels.
That’s not to criticise or belittle an incredible public service in the UK that, in my experience, offers outstanding healthcare services at zero or low cost to patients. The provision of care is peerless; it’s how the organization is administered that isn’t.
I recall hospital visits and physio sessions a few years ago when I suffered a leg injury where my appointments with different services in the NHS system exposed me to the admin side of things. While a particular specialist would be able to see my patient record on her computer screen, invariably she’d be unable to share that information digitally with other departments, or access information from my visits to those other departments.
Instead, it would be paper that would be shared containing information in hard copy (and handwritten) printed out from digital data. And all the various forms and documents I saw had a space at the top to affix a standard-size printer label with concise information about me: name, age, NHS number, etc.
Every file bundle that accompanied me on those visits also contained pages of blank labels, I imagine to be sure everyone had some.
I muse on these experiences today in the context of the ransomware cyberattack on Friday May 12 that has caused severe disruption to the NHS in England and Scotland.
It was one element in a global cyberattack that saw ransomware, a particular type of malware, known as WannaCry infect tens of thousands of Windows computers in 150 or more countries on Friday and into the weekend, reaching well over 200,000 machines by Sunday night.

- Background: WannaCry cyber attack on Wikipedia
- Analysis: Everything you need to know about the WannaCry / Wcry / WannaCrypt ransomware by Troy Hunt
Although Friday’s attack was largely stopped in its tracks, there’s prediction that more will likely come very soon according to alarm bells being rung over the weekend by Europol.
Companies need to make sure they have updated their systems and “patched where they should” before staff arrived for work on Monday morning, the EU law enforcement agency head said.
Such concerns were echoed by the Financial Times on Sunday.
According to web analysis by the cyber intelligence company Digital Shadows, more than 1.3m computers are still connected to the internet with the vulnerability in their file-sharing protocols unaddressed. “It’s only a matter of time before cyber criminals evolve the WannaCry ransomware malware to become even more virulent,” said Becky Pinkard, vice-president of service delivery and intelligence at Digital Shadows. “The SMB protocol [the vulnerability] is one that should never be allowed to be accessed from the internet anyway. As we have seen, this is allowing it to spread very quickly and it is causing havoc.”
Also on Sunday, reports began appearing that new variants of the ransomware had already started emerging. Writing in the Wordfence blog, Mark Maunder warned that this week will be “rough for Windows users”:
We expect new variants to emerge all week that continue to exploit the vulnerability in SMB that WannaCry has been using. It is critical that Windows users protect themselves immediately against this threat.
SMB stands for Server Message Block, the protocol typically used by Windows machines to communicate with file systems over a network.
So where does this leave organizations and individuals that were hit – and in the UK, especially the NHS – who are facing a potential nightmare of upgrading the operating system on their hundreds and thousands of Windows computers in very short order?
The Uncomfortable Reality
This attack only hit computers running Windows. If you have a recent version of Windows on your machines that still enjoys tech support from Microsoft – that’s Windows 7 and up – and those machines are bang up to date with all updates, patches, fixes, etc, provided by the Windows Update service or via an enterprise update deployment system within your own organization, then it’s very likely that you can breathe a sigh of relief that you aren’t directly affected by this event.
If you run Windows 10, you can breathe that sigh of relief straightaway as this latest version of Windows is immune from this particular type of attack, according to Microsoft.
But if you were not running any of the operating system versions mentioned and, instead, still ran Windows XP – a 16-year-old operating system, not generally supported by Microsoft since 2014 – then you were a prime target for this attack.
What the malware did was find Windows computers that had the specific SMB vulnerability that gave it access to those computers. Windows XP machines fit the bill perfectly. Once in, the program would execute and propagate itself to other connected machines like a virus.
In the case of the NHS, it seems very clear that some of the trusts in England and Scotland still run Windows XP; or, at best, a more recent version of Windows but one that hasn’t been fully updated with ‘critical’ or ‘important’ updates, specifically the patch that Microsoft released on March 14 that fixed the vulnerability exploited in Friday’s attack.
(Luckily for anyone else still running Windows XP, Microsoft released a patch late on Friday that will fix the vulnerability. Grab it now!)
Here’s how to tell if your PC has the patch already installed – this screenshot shows what appears in the list of installed Windows Updates on one of my laptops running Windows 7 SP1.
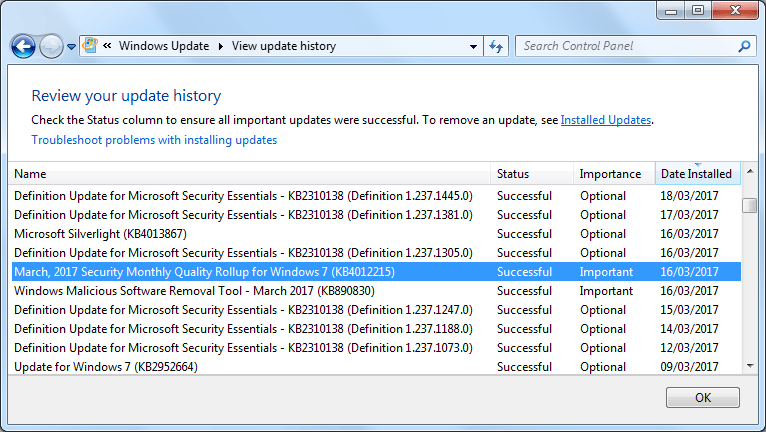
The entry to look for on a Windows 7 machine is “March, 2017 Security Monthly Quality Rollup for Windows 7 (KB4012215)” that would have been installed on March 16 or thereabouts if you have automatic updates turned on for Windows Update.
You may also see it in the updates listing as something like “MS17-010: Security update for Windows SMB Server: March 14, 2017.”
Is There The Will?
As Friday’s events graphically illustrate, the consequences of such blissful ignorance / lack of foresight can include the potential catastrophe of a cyberattack succeeding with results such as we’ve started seeing.
Of course, it’s a relatively simple matter to update your computer if you’re an individual or a very small business. If you’re an organization the size of the NHS, it’s a different matter altogether, one that’s time-consuming, expensive and complex.
In the case of the NHS, there are some serious politics involved here. The NHS is a huge organization employing 1.5 million people in the UK and with an annual budget of over £116 billion (£101 billion in England alone). Its prominent place at the heart of British society and the economy make it a subject of strong political involvement.
I don’t want to get into the politics of the NHS. It’s a significant issue for every political party campaigning for the general election that will take place on June 8, so you can get your fill of that in the mainstream media.
Still, what I will say is this. This specific technology issue currently causing havoc in the NHS needs addressing right now. There was a Windows custom support agreement in place with Microsoft, worth £5.5 million annually, that was last renewed in 2014. That implies there has been no support from 2015 onwards.
How those in charge of the NHS – the politicians, the managers – allowed this situation to happen undoubtedly will be the subject of much investigation. Late yesterday Microsoft added to the forthcoming debate in a blog post from its president and chief legal officer Brad Smith who criticised the way governments store up information about security flaws in computer systems, noting:
“As cybercriminals become more sophisticated, there is simply no way for customers to protect themselves against threats unless they update their systems. Otherwise they’re literally fighting the problems of the present with tools from the past. This attack is a powerful reminder that information technology basics like keeping computers current and patched are a high responsibility for everyone, and it’s something every top executive should support.”
In the meantime, the politicians need to magic up some money and the serious intent to get this sorted out immediately.
My musing about the NHS at the start of this article makes me think that serious intent is something in very short supply in government and at the NHS as far as ensuring IT systems safety and security are concerned. It shows a lack of intent and will in government no matter the party in power. And I note that this is the organization where government has spent £10 billion so far on a now-abandoned IT patient records system.
Looks like money that would have been better spent on more laser-printer labels.
Next Steps
If you read these words on Monday morning, it may well be too late to protect your networks if they are still vulnerable to a cyberattack of this nature. Meaning, if you’re running an unpatched installation of any Windows version from XP to 8.1 (you’re okay if you’re on Windows 10).
Version 1 of WannaCrypt was stoppable but version 2.0 will likely remove the flaw. You’re only safe if you patch ASAP.
— MalwareTech (@MalwareTechBlog) May 14, 2017
Other advice suggests disabling the Windows feature that provides the entry point on unpatched Windows computers for the malware to gain a foothold.
#WannaCry #ransomware If you can’t patch, disable SMBv1 –
Microsoft support:https://t.co/5hYgOfGzUG pic.twitter.com/dld06sYQDn— Patrick Coomans (@patrickcoomans) May 13, 2017
That at least might buy you some time while you get your machines either patched or upgraded as a matter of extreme urgency.
And last but certainly not least – be proactive and open in your communication about your state of defence, especially within your organization. There will be a lot of worried and confused employees and others who will need knowledge and understanding that help guide them in supporting your initiatives.
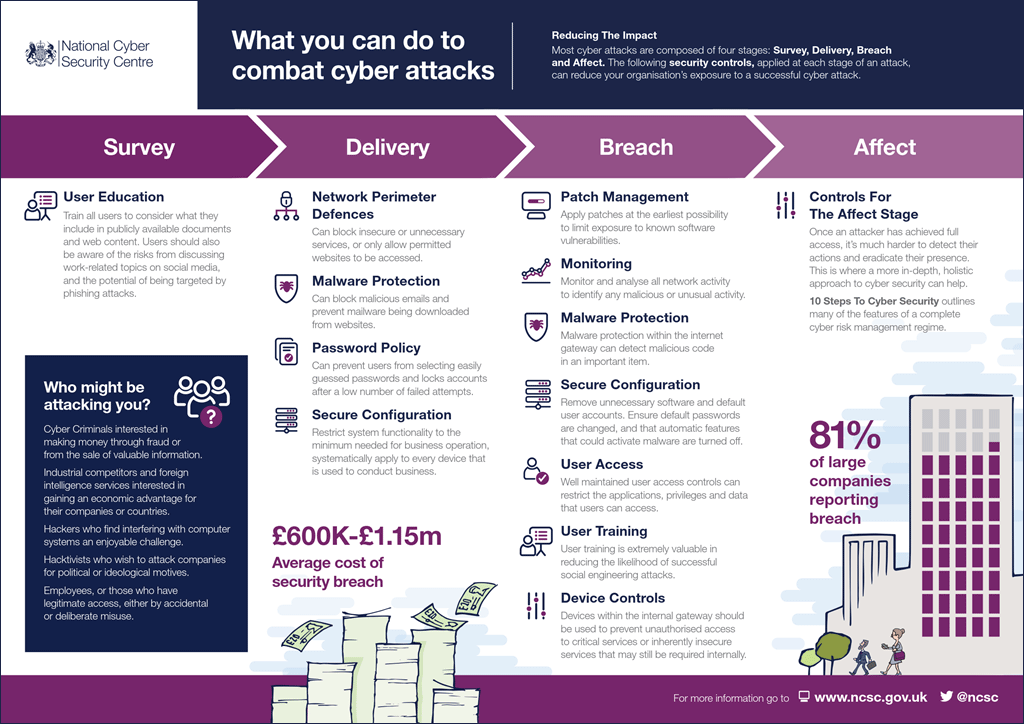
The National Cyber Security Centre has some excellent infographics and other content that you may find helpful, like this one on common cyber attacks. Note the concise advice on communication.
(Map of countries hit via BBC News)